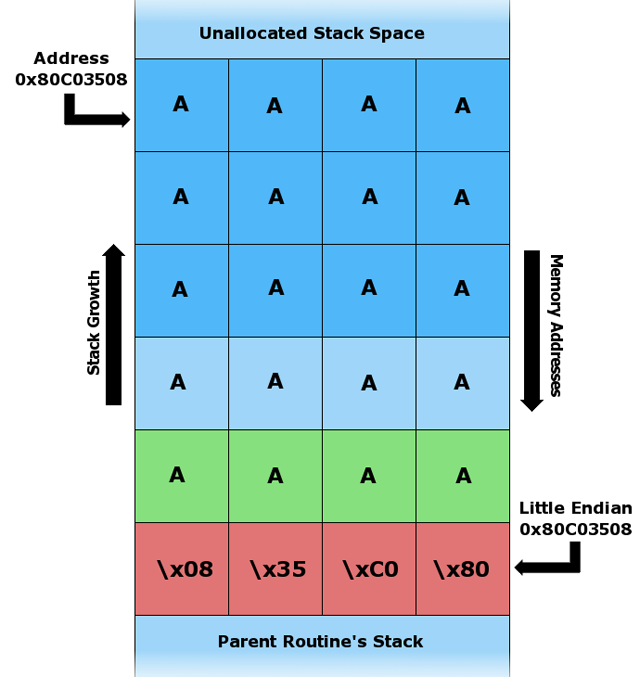
Diagram showing attacker overwriting a return address with a pointer to the stack that contains attacker-supplied data
The latest release of Google's Android mobile operating system has finally been properly fortified with an industry-standard defense. It's designed to protect end users against hack attacks that install malware on handsets.
In an analysis published Monday , security researcher Jon Oberheide said Android version 4.1, aka Jelly Bean, is the first version of the Google-developed OS to properly implement a protection known as address space layout randomization. ASLR, as it's more often referred to, randomizes the memory locations for the library, stack, heap, and most other OS data structures. As a result, hackers who exploit memory corruption bugs that inevitably crop up in complex pieces of code are unable to know in advance where their malicious payloads will be loaded. When combined with a separate defense known as data execution prevention, ASLR can effectively neutralize such attacks.
Although Android 4.0, aka Ice Cream Sandwich, was the first Android release to offer ASLR, the implementation was largely ineffective at mitigating real-world attacks . One of the chief reasons for the deficiency was Android's executable region, heap, libraries, and linker were loaded at the same locations each time. This made it significantly easier for attackers designing exploits to predict where in memory their malicious code can be located.
"As long as there's anything that's not randomized, then it (ASLR) doesn't work, because as long as the attacker knows something is in the same spot, they can use that to break out of everything else," Charlie Miller, a veteran smartphone hacker and principal research consultant at security firm Accuvant, told Ars. "Jelly Bean is going to be the first version of Android that has full ASLR and DEP, so it's going to be pretty difficult to write exploits for that." Miller has spent the past seven years writing software exploits that can install malware on Macs, iPhones, and Android handsets when they do nothing more than browse a booby-trapped website.
By contrast, Apple's competing iOS has offered fully implemented ASLR and DEP for the past 16 months. Not that Apple developers' track record of adding the protection has been perfect. The 2009 debut of OS X Snow Leopard also failed to randomize core parts of the OS . Those omissions were finally fixed with the later release of OS X Lion.
Unlike its Android predecessors, Jelly Bean provides randomization for what's known as position-independent executables. That will make it significantly harder to use a technique known as return-oriented programming when exploiting buffer overflows and other memory-corruption vulnerabilities discovered in the mobile platform. Jelly Bean also provides defenses to prevent information leakage exploits that can lead to much more serious OS exploits.
Android has yet to introduce code signing, a protection designed to prevent unauthorized applications from running on the device by requiring code loaded into memory to carry a valid digital signature before it can be executed. It has long been present in iOS


